An Overview of Security Firewall Types
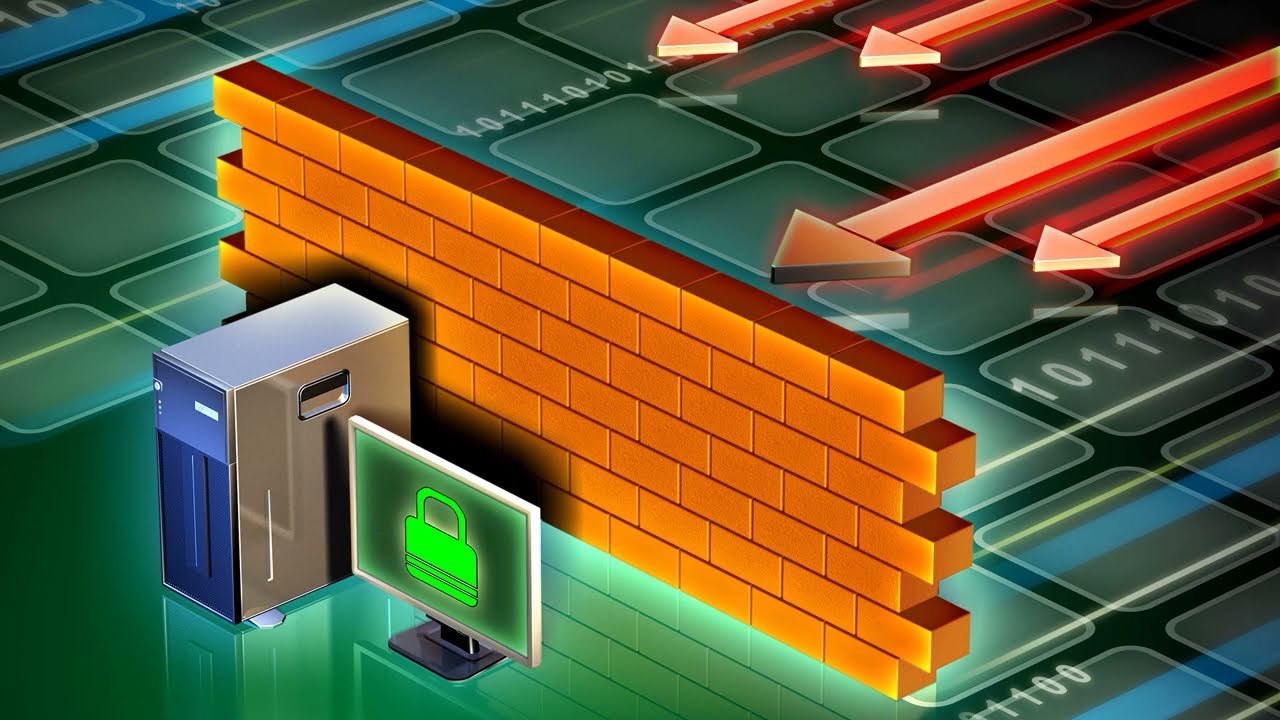
Whether you are a novice in the IT security world or simply looking for a better understanding of what firewalls do, many different types exist. This article will discuss Host-based, Network-based, Proxy, and Next-generation firewalls. These firewalls are designed to protect your computer against many threats.
Host-Based Firewalls
Whether using a personal computer or running a business, a host-based security firewall can answer your security problems. The firewall can protect you from malware attacks and other threats that may try to infect your computer.
A host-based security firewall is a computer software application that monitors the traffic in and out of a particular host, how does a firewall work? The firewall also allows you to restrict outgoing network traffic wherein. It can also be used to control software used on your PC.
A host-based security firewall can help you avoid malware infections and denial-of-service attacks. In addition, the host-based firewall can prevent malicious network service worms from connecting to your network.
Many anti-virus companies include a firewall with their anti-malware programs. However, it is essential to configure the firewall properly to ensure it is effective. Not doing so can prevent you from protecting yourself from the most common malware exploits.
To configure a host-based security firewall, you need to understand its architecture. You’ll need to determine which network interfaces you want to protect and which you want to deny. You can then use a tag-based policy to steer traffic toward the correct interface. This is a simple way to apply a firewall intent, and it’s more effective than service chains.
The host-based security firewall is also an excellent micro-segmentation tool. You can customize it to protect a specific device, such as a desktop, laptop, or server.
Network-Based Firewalls
Depending on your requirements, network-based security firewalls can be an effective tool to protect your network. There are many types of firewalls, including hardware and software appliances. They may be integrated into your network’s architecture or installed as an external device. They are usually installed at the edge of your network and are designed to provide good performance.
When a firewall receives a packet, it is inspected to determine whether it should be accepted or dropped. The decision is based on the packet’s source and destination IP addresses and the firewall’s rules. For example, if a package comes from a remote server, the firewall may check if the destination IP address is a valid DHCP address. If not, the packet will be dropped.
The same principle applies to host-based firewalls. A host-based firewall is typically a part of an operating system. Therefore, they are easy to maintain and protect hosts from attacks.
Regardless of which type of firewall you choose, you should ensure it meets your organization’s needs. For instance, you may need to monitor a web application’s traffic to detect unauthorized access. You can also use firewall logs to see unwarranted configuration changes. You can also schedule automated systems to automatically check for new updates and implement them when necessary.
You should also consider using a host-based firewall for protection from a compromised host. This will protect your host from unauthorized access, but you must configure your firewall to turn it off if a compromised host is in the same network.
Next-Generation Firewalls
Unlike traditional firewalls, which only inspect packets and ports, next-generation security firewalls offer a wide range of functions. They provide comprehensive visibility into your network’s traffic and are flexible enough to adapt to changing threats.
They are also designed to protect against new, advanced, and persistent threats. Some even offer protection systems and awareness tools. They can be deployed on-premise or in the cloud. They can be configured to work with different user roles and environments. They can also integrate with threat intelligence services to give you a comprehensive view of your network’s threats.
Another feature regularly used is intrusion protection. It enables you to identify the source IP addresses where attacks come from and provides information about IP reputation. It can help to improve packet-content filtering as well.
Next-generation firewalls can detect malware and identify malicious IP addresses before they can enter your network. They can also see abnormal behavior, such as irregular deviations from everyday activities.
These appliances are not only more affordable and more accessible to maintain than traditional firewalls, but they are also more effective at blocking cyber attacks. In addition to detecting malware, they can also thwart advanced persistent threats.
The next-generation firewalls use static and dynamic packet filtering and have an application-awareness tool. In addition, they can translate network addresses and offer VPN support.
Proxy Firewalls
Firewalls are software applications that monitor, inspect and filter all incoming and outgoing network traffic. They protect networks from attacks by detecting and blocking suspicious activities. They can be used in corporate environments and consumer settings. They can be installed at the perimeter or inside a network to prevent internal and external threats.
Firewalls can perform Network Address Translation, or NAT, which hides internal IP addresses from outsiders. They can also block specific services or applications from accessing information. They can also be used in tandem with a VPN, which hides the IP addresses of internal servers from the Internet.
A firewall will protect a network from malware, eavesdropping, and other cyberattacks. It can identify and block malicious requests that come from trusted sources. They can also be used to restrict workplace web browsing to keep employees from viewing content that could be considered inappropriate.
They are commonly used in corporate settings to prevent insider attacks. Generally, they block data packets based on pre-established security rules. Unfortunately, however, they are also sometimes misused in ethically questionable ways.